[section label=”Introduction”]
Enterprise Class Router at a Consumer Class Pricepoint
 Several days ago, we got our first glimpse into Ubiquiti’s enterprise networking gear lineup when we reviewed the Ubiquiti UniFi AP AC PRO, an impressive Wi-Fi access point which delivered enterprise class performance and enterprise class features at a reasonable price.
Several days ago, we got our first glimpse into Ubiquiti’s enterprise networking gear lineup when we reviewed the Ubiquiti UniFi AP AC PRO, an impressive Wi-Fi access point which delivered enterprise class performance and enterprise class features at a reasonable price.
Today we’ll be reviewing a significantly different product in the Ubiquiti UniFi lineup, the Ubiquiti UniFi Security Gateway (USG), which despite its name implying that it’s purely a firewall appliance, is actually a combination of an enterprise class router along with firewall capabilities.
Specifications
| Manufacturer | Ubiquiti |
|---|---|
| Model | UniFi Security Gateway |
| Processor | Cavium Octeon+ CN50xx Dual-Core 500MHz, MIPS64 with Hardware Acceleration for Packet Processing |
| RAM | 512MB DDR2 |
| Storage | 2GB |
| Layer 3 Forwarding Performance | 1,000,000 pps (64 Bytes), 3Gbps (512 Bytes or Larger) |
| Network Interfaces | Three 10/100/1000 Ethernet |
| Additional Ports | RJ45 Serial Port |
| Power Draw | 7W |
| Dimensions | 135mm x 135mm x 28.3mm |
| Weight | 366g |
| Check Pricing | Click Here |
Taking a quick look at the specifications, we can see that the Ubiquiti USG is very much an entry level routing/firewall appliance. Despite being powered with an older Cavium Octeon+ CN50xx series dual-core 500MHz processor paired with 512MB DDR2 RAM, Ubiquiti claims the USG is capable of routing up to 1,000,000 pps (Packets Per Second) for 64 Byte sized packets and 3Gbps for 512 Bytes or larger transfers. Additionally, thanks to the lower power components, power consumption comes in at a mere 7W.
Let’s take a closer look.
[section label=”A Closer Look”]
A Closer Look
Here’s a look at the packaging for the Ubiquiti UniFi Security Gateway (USG).
Included in the packaging is a quick start guide, a power adapter, a small bag of mounting screws (two screws, two anchors not shown) and the UniFi Security Gateway.
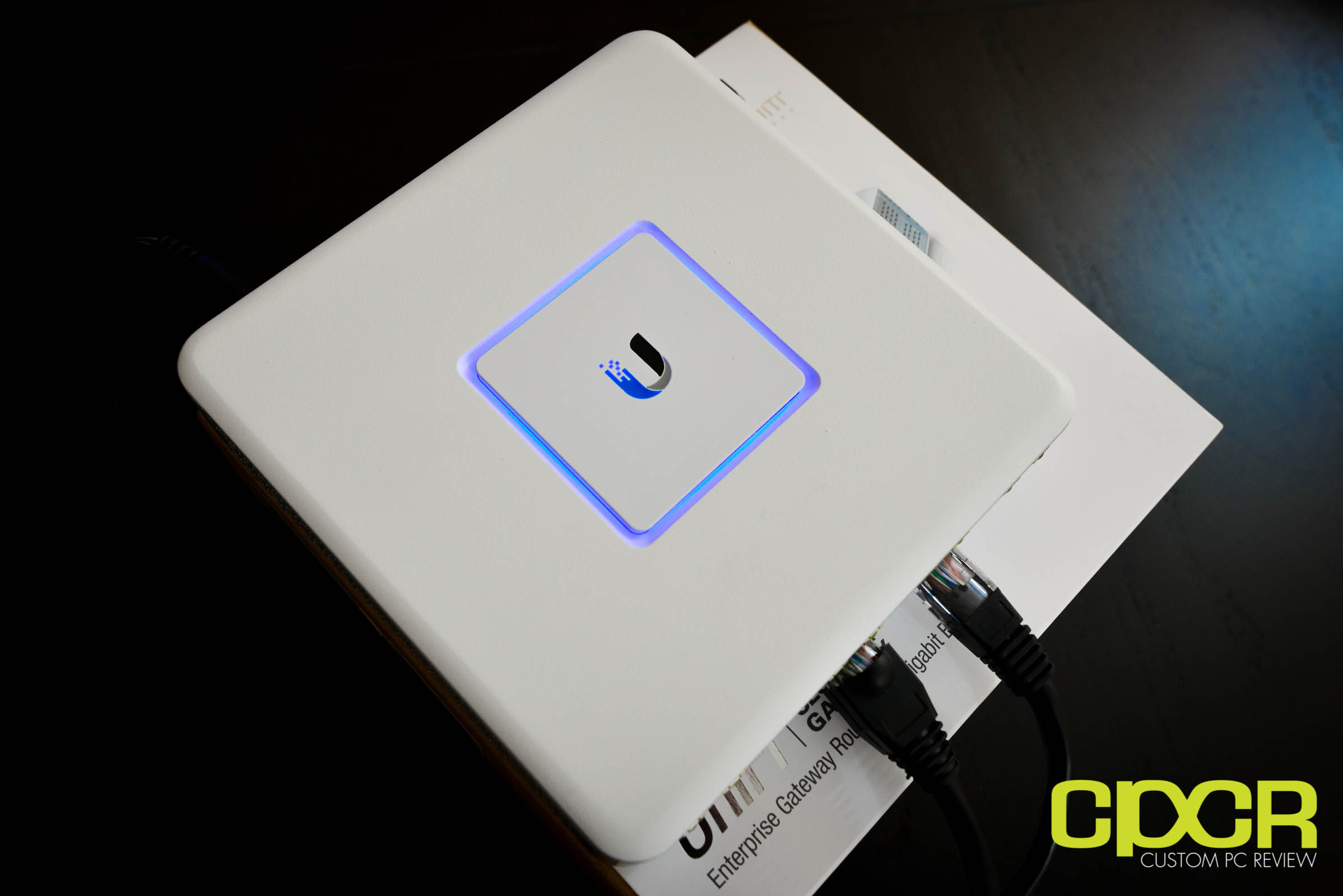
The Ubiquiti UniFi Security Gateway (USG) is a small, four port device measuring 135mm x 135mm x 28.3mm. I/O includes one dedicated console port and three 10/100/1000 Gigabit Ethernet ports. The Gigabit Ethernet ports from left to right are labeled WAN, LAN, and VoIP although those comfortable using a CLI based interface can set these ports to do anything.
Once the UniFi Security Gateway is plugged in, the status indicator LED square will begin to glow. Here’s a list of all the different status indicators available.
| Light Description | Status |
|---|---|
| White | Fully Booted; Not Adopted |
| Blue | Adopted and Provisioned |
| Alternating White/Blue | Device Firmware is Upgrading |
| Blue Flashing | Device Locator Activated from UniFi Controller |
[section label=”UniFi Controller”]
UniFi Controller
Like the rest of the Ubiquiti UniFi product lineup, the Ubiquiti USG is administered using the UniFi Controller software or via the CLI (Command Line Interface). The benefit of USG supporting UniFi Controller is that depending on your requirements, it could potentially be managed entirely through the GUI.
The UniFi Controller software can be hosted either locally on a system/server at your location or on a remote server/cloud instance. Ubiquiti also sells the Ubiquiti UniFi Cloud Key which is a bit like a hybrid solution in that it will act as a dedicated local UniFi Controller and because it connects to Ubiquiti’s cloud, users can perform remote management of the system as well.
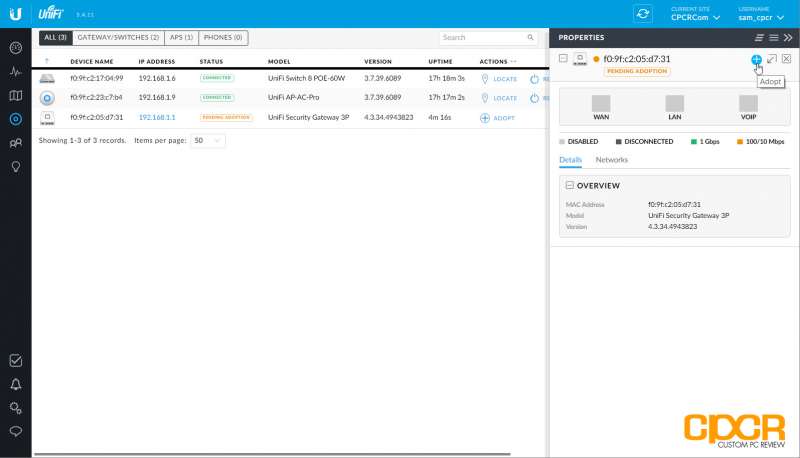
Setting up the USG to work with the UniFi Controller is a fairly painless experience. Once the UniFi Controller is fired up, simply go to the devices tab in the controller and all devices detected on the network should show up. The UniFi devices that are ready to adopt will let you know that they’re pending adoption. Simply click on the device and click adopt on the device menu afterwards.
Here’s a look at the main interface screen once logged in to the UniFi Controller. With a complete UniFi system, Ubiquiti has made it very easy to quickly check the status of the network.
At the top right, we can see three large green circles: one for WAN, one for LAN, and one for WLAN. This signifies everything is good to go. At the top left is some performance numbers from speedtesting while the middle and bottom section shows statistics on the network.
The USG can be configured by clicking on the device under the device screen. This allows monitoring and configuration for the specific device. This includes details on the device, the networks it’s connected to, and configuration of the WAN, port forwarding, DDNS and firmware updates.
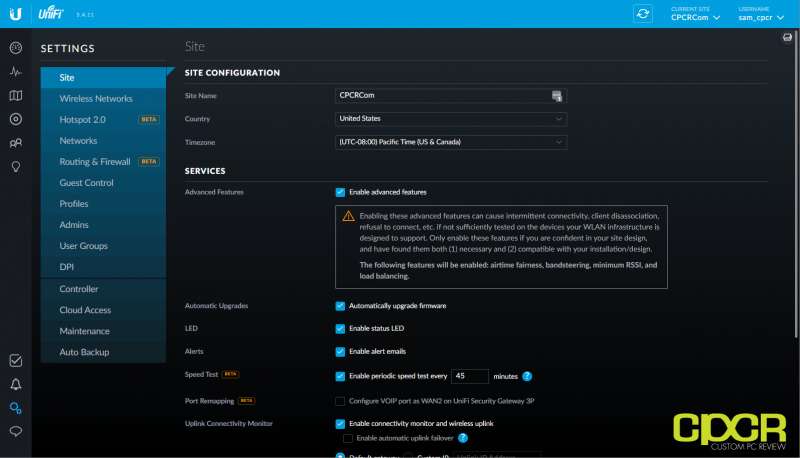
Going into the site settings is done simply by clicking on the two gears at the bottom left. From here, we can do most of our configuration. Unlike most consumer or small business routers, the reason why the UniFi routers are configured by site is because the UniFi system is designed to be deployed with multiple routers, switches, and access points so this makes it easy to reconfigure everything all at once by setting up a single site configuration.
The main settings for the USG is pretty much the networks, static routes and the firewall configuration. These can all be setup through the GUI.
Some other crucial settings such as QoS is unfortunately left out.
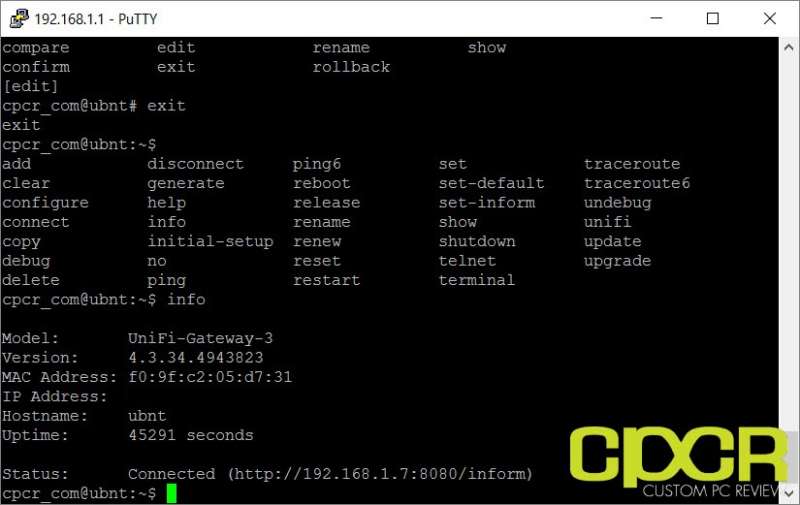
Luckily, many options not available through the GUI can be done through the CLI which can be accessed via the console port or through SSH. The USG utilizes EdgeOS which is a fork of Vyatta’s OS which is now owned by Brocade. EdgeOS however is the same OS as you’d find in many of their other products such as their EdgeRouter series. As such, most of the CLI commands from the EdgeOS guide or even Vyatta can be applied to the USG.
Finally, one of the biggest selling points for the USG is the Deep Packet Inspection (DPI) feature. With DPI enabled, all sorts of traffic statistics can be found such as where the majority of traffic is going, what protocols are used, etc. While not so much a big problem on smaller networks, network administrators on bigger and busier networks can use the data to figure out how to shape traffic in order to ensure a good network experience for everyone.
[section label=”Performance”]
Performance
Firewall Performance
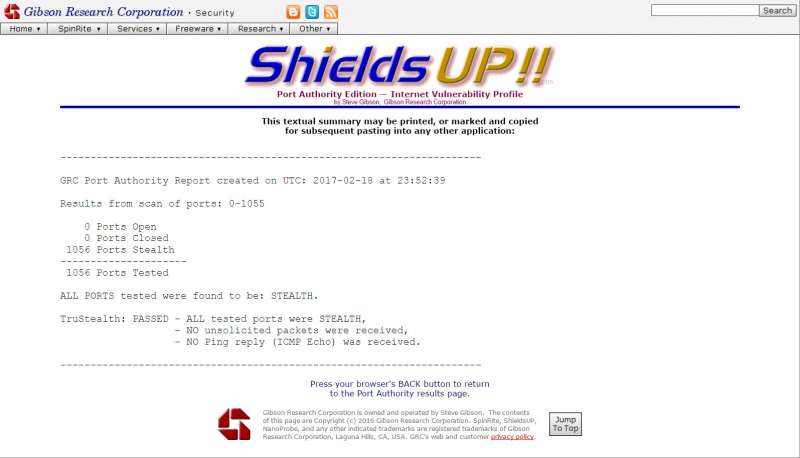
For the most part, a firewall for a home or small business network should simply prevent people from the WAN from finding open ports and finding out that a network exists at a certain IP. Most hackers are simply using automated software to find networks with vulnerabilities, so this is the most important job for a firewall. The default firewall rules for the USG ensured that this was mostly the case. One issue I did experience is that Ubiquiti left ICMP (Ping) from WAN enabled by default which had to be disabled via the CLI interface.
Once disabled, the USG should be secure enough for most home network deployments. In order to test this, I utilized GRC’s Shields Up online security test to confirm this.
For those looking for additional security beyond this such as IDS/IPS functionality, anti-virus, proxies, etc. will still require something like a PFSense solution.
Routing Performance
Routing performance is tested using two systems. The first is a server using an Intel PRO/1000 Dual Port Server Adapter EXPI9402PT is connected directly into the WAN port of the router. The second is a client using an Intel PRO/1000 Dual Port Server Adapter EXPI9402PT is connected directly to the first LAN port on the router. Transfer speeds between the systems are then tested using iPerf 3.1.3.
Performance Analysis
Looking at performance for the Ubiquiti USG, it was able to achieve a WAN to LAN performance of 928Mbps making it one of the fastest routers we’ve tested, coming in just slightly behind the Synology RT2600ac.
With Deep Packet Inspection enabled, the performance of the Ubiquiti USG does incur a slight performance loss as performance dropped to 826Mbps. While this is a fairly significant performance loss, it should still be more than adequate for those on less busy residential or small business connections.
[section label=”Conclusion”]
Conclusion
Overall the Ubiquiti USG is yet another excellent product from Ubiquiti. It’s powerful, it’s fast, it’s reliable, it has a wide feature-set and it’s a great looking piece of equipment as well.
The only issue I had with the USG is just the fact that it comes by default with ICMP (Ping) on WAN enabled and disabling it requires going into the CLI. That said, it’s a very easy solution and a quick search into the Ubiquiti forums will provide a solution.
What I did find slightly more difficult however, is setting up QoS settings for gaming and Wi-Fi calling. Unfortunately, this meant spending a lot more time in the CLI and the Ubiquiti forums than I would’ve liked however, it’s also not terribly difficult since I have some prior experience with iOS and Junos. That said, if you’ve never worked on a CLI before and stuff like QoS is something that you really need, you will probably need to spend some time researching to get stuff configured the way you like. If that doesn’t sound appealing to you, you could potentially be better off with something a little more user friendly.
Pricing on the Ubiquiti UniFi Security Gateway (USG) is currently $112.50, which is a very good pricepoint for a piece of equipment like this. Similar solutions from other vendors such as Cisco cost several times the pricetag yet in some cases don’t even offer the same level of performance the USG does.
Ultimately, the USG is a good product at a good price, but what ultimately sets it apart is its ability to integrate into the UniFi ecosystem. If having a USG fill the UniFi Controller interface with tons of information is what you’re looking for, then the USG is the obvious way to go. However, if being able to manage the system remotely doesn’t matter nor does having full integration into the UniFi Controller software, Ubiquiti already sells the Ubiquiti EdgeRouter Lite, which aside from the exterior appearance is the same exact thing as the USG without the UniFi Controller integration, but can be picked up for even less than the USG.
Sample provided by: Ubiquiti
Available at: Amazon



























Nice streaming site stats ;)
Glad to see at least someone is reading through the whole review. =)
So.. would I still need the Cloud key device as a controler or can the Ubiquiti UniFi Security Gateway do that part?
Yes, you’d still need a cloud key or utilize a dedicated PC as a controller.
Thanks! Good review